This year I’ve attended the hack.lu conference in Luxembourg. Being actually for the first time there, I’ve had absolutely no expectations. In fact it was a really lovelly and warm athmosphere during the whole conference and I’ve met a lot of interesting persons.

A nice @hack_lu logo made with the @Level2Lu 3d printer during #hacklu. pic.twitter.com/jFB1wlw5uS
— hack_lu (@hack_lu) October 18, 2016
Talks #
I think there were some realy good talks. Unfortunately I’ve seen only 1 because most of the time I was at the workshops practicing my reverse engineering skills. If you want to know more about the talks, read here:
If you’re looking for the talks, have a look at this channel.
Workshops #
Below the workshops I have attented:
Advanced Exploitation: ROP #

Ready for tomorrow’s workshop on ROP exploitation at @hack_lu @KudelskiSec pic.twitter.com/M5F2F2V44N
— Julien Bachmann (@milkmix_) October 17, 2016
The Advanced Exploitation: ROP and protections bypass under Linux course by Julien Bachmann was my first one and very good. It’s not that I haven’t heard of ROP (Return Oriented Programming) before, it was rather a lack of time which prevented me going deep-dive into this specific topic. After refreshing knowledge how programms get executed and how function calls are working, basic exploitation techniques like stack based overflows were introduced to the audience. Debugging frameworks like GEF and PEDA were shortly explained and used to examine the stack and registers during the exploitation.
Thereafter the basic ideas behind ROP were presented: Instead of bringing sth into the process, ROP will use pieces of code fragments inside the process to conduct the attack. That means: In a classical stack based overlow attack one will try to overlow some buffer, control the return address of a function and put some code (shellcode) on the stack that might get executed. Binary exploitation countermeasures like ASRL or NX have introduced new methods how to protect against such attacks. However, new exploitation techniques have been found to circumvent those. Starting with ret2libc ROP gadgets were basically the further development. The main idea behing ret2libc was to call libc functions directly instead of using syscalls. In this case the calling convention (how to push the parameters for the function into the stack) had to be taken into account. Finding some good examples on the net should be not that hard.
In the world of ROP specific code fragments have to be used in a certain order to build a ROP chain. That means that by pushing some data (mostly addresses) into the stack and having a buffer overflow we can control the program execution depending on the data being pushed into the stack.
Make sure to have a look at https://speakerdeck.com/milkmix/advanced-exploitation-on-linux-rop-and-infoleaks for more detailed explanations.
Finding ROP gadgets is actually also an easy task. There are several tools which will help you finding those:
Some of the useful gadgets would be:
- redirect execution to address pointed by some register
- stack pivot (change the original stack to sth different; that might be the heap)
- set register values
- read at a memory address
- “write-what-where”
- syscall (
int 0x80for x86)
Julien also provided live examples for ROP exploitation. Make sure you do have a look at https://github.com/0xmilkmix/training. All in one this was an excellent introduction to ROP which during the 4h course provided enough information to be “armed” for your next target. Probably I would have spent more than 2 weeks to accumulate the same amount of information. A big thanks to Julien his training and explanations.
The Fantastic 4 forensic domains: net, disk, mem, mal #
This workshop aimed at showing the audience some techniques and tools when it comes to DFIR. Having some data provided by the NATO Cooperative Cyber Defence Centre of Excellence David and Christophe started looking at different aspects:
- network traffic
- disk data
- memory data
- malware activities
Rather than covering each aspect individually, a more interdisciplinary approach was prefered. By analysing the input sources and correlating the results with some others would bring you more benefits than focusing only on a single task. Among some tips how to deal with the data source, some tools mentioned as well:
- AccessData FTK Imager
- saves an image of a hard disk in one file or in segments
- log2timeline
- check out the presentation
- helps creating super timelines (correlation, context, confidence, sorted based on time)
- rekall
- I know everybody knows about volatility
- but
rekallshould be faster
One thing that caught my attention was the fact that when doing string analysis, you can use old good strings also for unicode strings:
|
|
From the manpage:
|
|
Nice. Also make sure you’ll have a look at the presentation and the provided data sources. Happy DFIR!
Android malware reverse engineering #

Ready for the #Android #RE #workshop at #hacklu ;) cc: @Fortinet pic.twitter.com/gIClXygRUz
— Axelle Ap. (@cryptax) October 14, 2016
Axelle Apvrille had a workshop on Android Malware Reverse Engineering. While the first part covered the “basics” (static code analysis and dynamic analysis) not that interesting to me (due to previous work: here, here and also here) the second part dealed with obfuscation and packed samples.
Installing the workshop VM (ca. 5 GB) was also quite easy:
|
|
Like mentioned before the 2nd part of the workshop was rather the fun part. By structuring the whole workshop in several labs, the students were able to dissect the APKs locally and play with the provided tools. In lab 6 e.g. we had to analyze an infected version of Pokemon Go by using AndroGuard. Students were then asked to deobfuscate some code fragments (sth that I did when analyzing FakeBanker). Then several unpacking techniques were shown:
- unpacking Pangxie
- unpacking via memory dump (files were packed by LIAPP)
One tool I’d like to mention when it comes to decompiling is JEB. It really helps you analyze your target using a nice GUI and it is extensible: Using Java or Python you can write your own scripts to automate the reverse engineering process.
If you don’t know which packer has been used APKI might be helpful. BTW: The rednaga team also haves an Android training. Make sure you’ll have a look at their materials. They’re really good.
All in one this was a very good workshop. Using the mentioned techniques you should be able to reverse DEX files easily. In case of JNIs you’ll have to go back to binary analysis since a malware could hide its all components inside a shared object (ELF). Besides that there is also ART which basically converts the bytecode into machine code (sampled inside an OAT file). Regarding ART: This video will give you a nice introduction.
ARM Shellcode Basics #
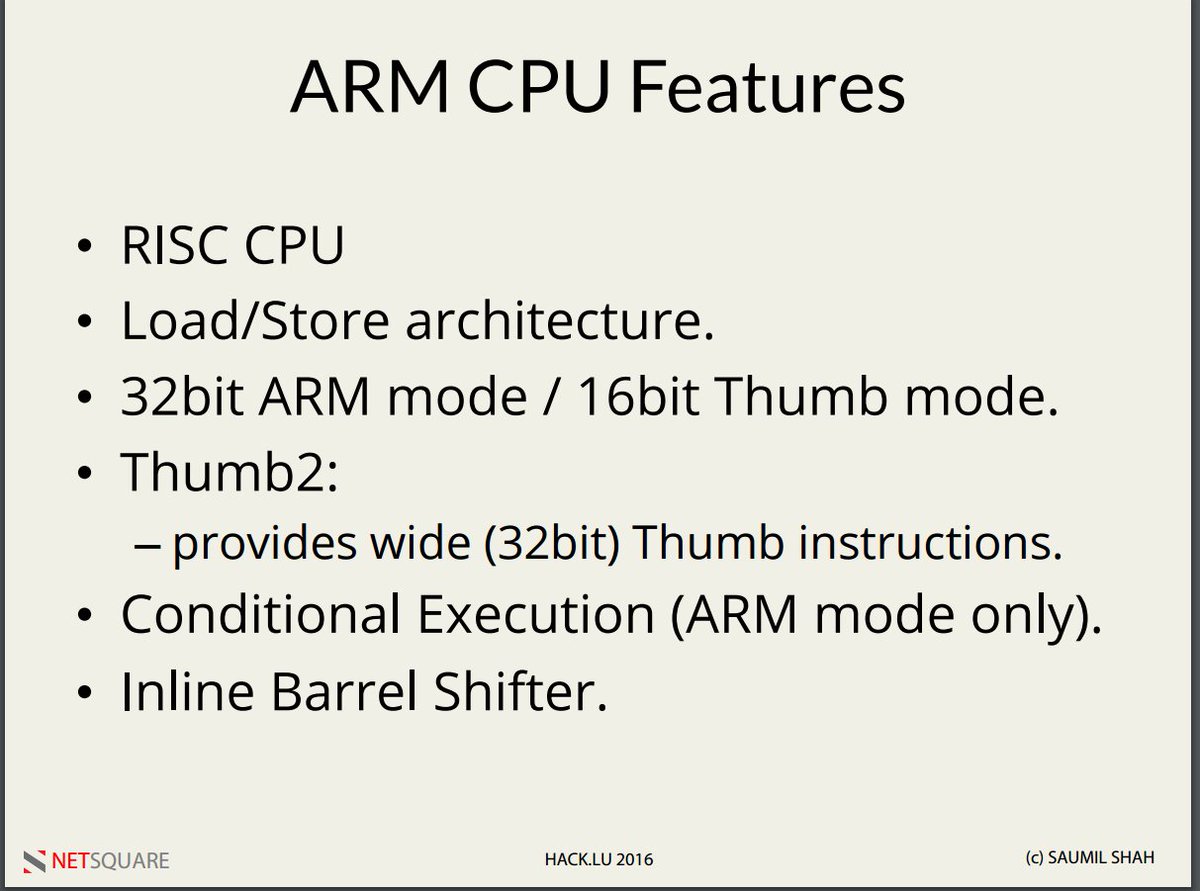
I think this one was my favourite one. Saumil Shah introduced to the basics of the ARM architecture before he got into the ARM Shellcode Basics. Again I’ve learnt a lot about ARM in just few hours.
Introduction to ARM Shellcoding by @therealsaumil Great! #hacklu pic.twitter.com/DOjLL5TbAp
— Victor Dorneanu (@victordorneanu) October 20, 2016
During the workshop we were able to write and run ARM assembly on a Raspberry Pi Saumil provided. This way we were able to test and run the shellcodes on real ARM hardware without any emulators.
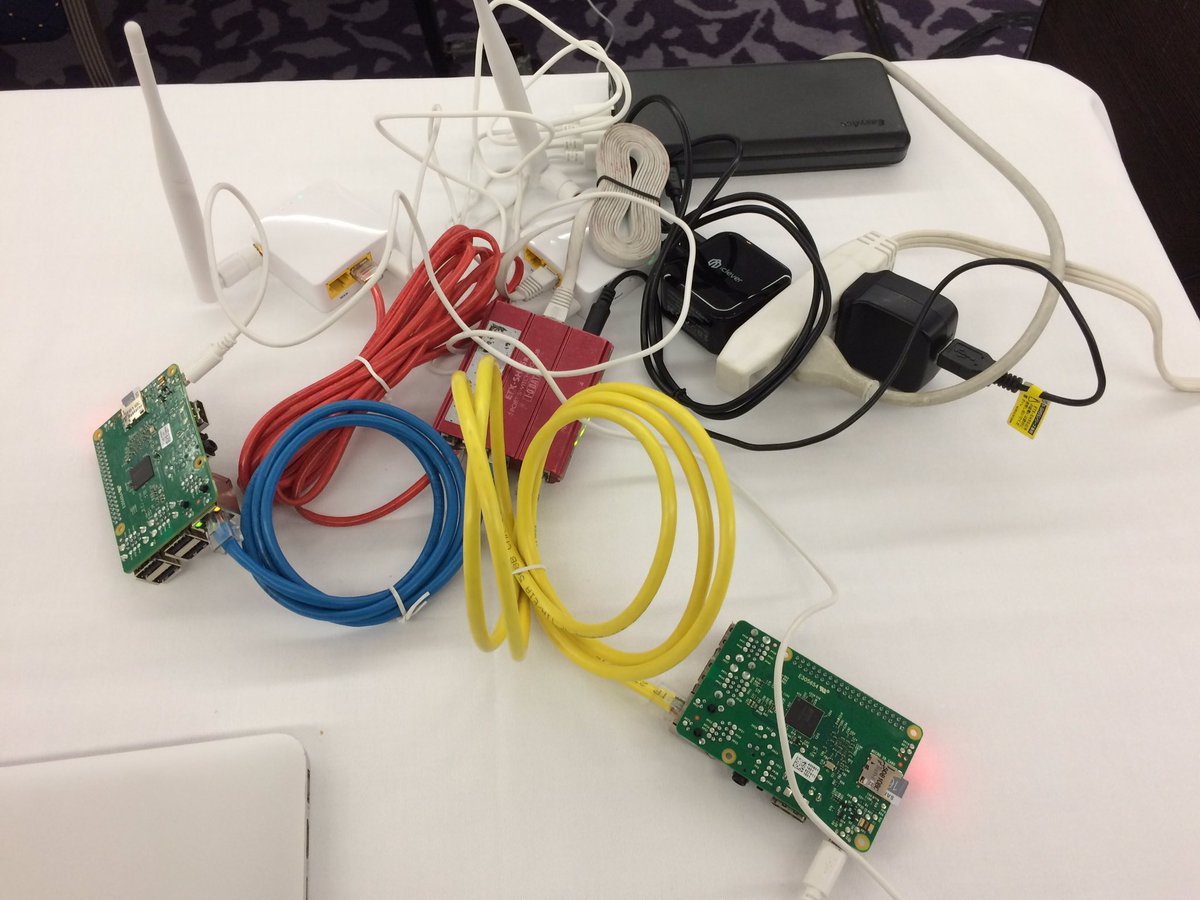
ARM Shellcode Workshop #hacklu - my mini Raspberry Pi NOC, with battery backup pic.twitter.com/FoOrH2p5ze
— Saumil Shah (@therealsaumil) October 20, 2016
After the workshop the difference between ARM mode and Thumb mode seems to be much more clear. Also the fact that most of the ARM shellcodes are in thumb mode was discussed extensively.
Writing ARM shellcodes doesn’t differ that much from the x86 way. Being equipped with good knowlegde how syscalls work on ARM and which parameters you need to use insde the registers (in ARM you don’t push the arguments on the stack) you should be able to write your very first shellcode. In fact it is much easier to write ASM assembly due to the small instruction set (you do have a lot of variations but the set is much smaller than the x68 one). Just one example:
|
|
Switching between the modes is also very simple:
|
|
However, de-NULLyfing the shellcode requires a good knowledge of the instruction set and how ARM works. A more complicated shellcode (reverse shell) was also shown and aimed at understanding how one would write more complex shellcode. As a next step (was not part of the workshop) one could dive deeper and write ROP gadgets for ARM. Now being more clear about how ROP works (see the workshop from Julien) this should be a very good exercise. ALl in one this was also a very good workshop and Saumil is really competent hacker and speaker. Next year he will be presenting some advanced ARM based exploitation techniques at the recon 2017 in Brussels.
Conclusion #
I think it was a really successful conference with really cool people and a nice location. I’ve really enjoyed the conversations I’ve had, especially during the refreshment breaks. Even though I haven’t manage it to see that many talks (actually only 1 - don’t blame me for this), I think my learning curve after the workshops I’ve attended was pretty straightforward.
I would like to thank all the Key Super Secret Company guys for letting me join their dinner. If you guys are reading this here, I hope to see you soon in Berlin :) And a big thanks goes to my Holy Romanian Water connection: I had so much fun with you (we somehow managed it to get back to the hotel :D)! To the Canadian fraction: Enjoy your trip and keep an eye for the big things (Sergei, ya know what I mean :P) And last but not least a warm hug for my Romanian fellows for sharing their skills in dissecting… bronies! And yes (how could I forget this?): Thank you hack.lu for organizing the whole stuff! I hope to see you next year again.
Some random images #
Some random images took during the days:




